Streamlining Application Infra Deployment: Advanced Practices & Adoption
Advanced practices, execution flows, and adoption strategies for modern infrastructure deployment. Part 3 of the 'DevOps and IaC Foundation' series.
What You’ll Learn
- How to activate end-to-end GitOps execution
- How to run push, PR, and approval-driven deployment models
- How to operationalize security, cost, and compliance
- How to drive adoption across teams without slowing delivery
- How platform teams scale IaC without becoming bottlenecks
1. From Foundation to Platform
In Parts 1 and 2, we designed principles and architecture.
Now we focus on execution and adoption — where most IaC programs succeed or fail.
This chapter shows how to:
- Convert repo structure into automated workflows
- Operationalize GitOps at enterprise scale
- Balance safety with developer velocity
- Drive platform adoption across dozens of teams
Goal: Turn infrastructure automation into a product — not a project.
2. GitOps Activation Using Azure DevOps Service Hooks
Goal: Make Git the control plane — every infrastructure change flows from version control, not tickets or consoles.
Azure DevOps does not provide a native webhook listener for arbitrary pipelines, so a lightweight webhook receiver (usually PowerShell or Python) is deployed inside the pipeline orchestration repo.
2.1 How It Works
- Developer pushes or opens PR in an application repo
- Azure DevOps Service Hook fires event
- Custom webhook listener:
- Validates repo + branch + path
- Resolves target pipeline template
- Injects metadata (app, env, service)
- Standardized pipeline executes
Git becomes the trigger, the audit trail, and the approval surface.
2.2 Why This Matters
- Eliminates manual pipeline selection
- Enforces consistent execution
- Enables zero-touch automation
- Keeps pipelines generic and scalable
Takeaway: Webhooks turn Git into a real control plane — not just a source repo.
3. Enabling Enterprise-Grade Azure DevOps Extensions
Goal: Shift risk detection left — before infrastructure reaches production.
Core Extensions
- Infracost — cost visibility before apply
https://marketplace.visualstudio.com/items?itemName=Infracost.infracost-tasks - GitLeaks / CredScan — secrets detection
https://marketplace.visualstudio.com/items?itemName=Foxholenl.Gitleaks - SARIF Report Publisher — security scan reporting
https://marketplace.visualstudio.com/items?itemName=sariftools.scans - Terraform CLI Tasks — standardized Terraform execution
https://marketplace.visualstudio.com/items?itemName=JasonBJohnson.azure-pipelines-tasks-terraform - Terraform Output — structured output extraction
https://marketplace.visualstudio.com/items?itemName=JaydenMaalouf.terraform-output
Tools don’t make platforms — guardrails do. These extensions operationalize guardrails.
Takeaway: Every PR should surface security risk, cost impact, and policy violations — automatically.
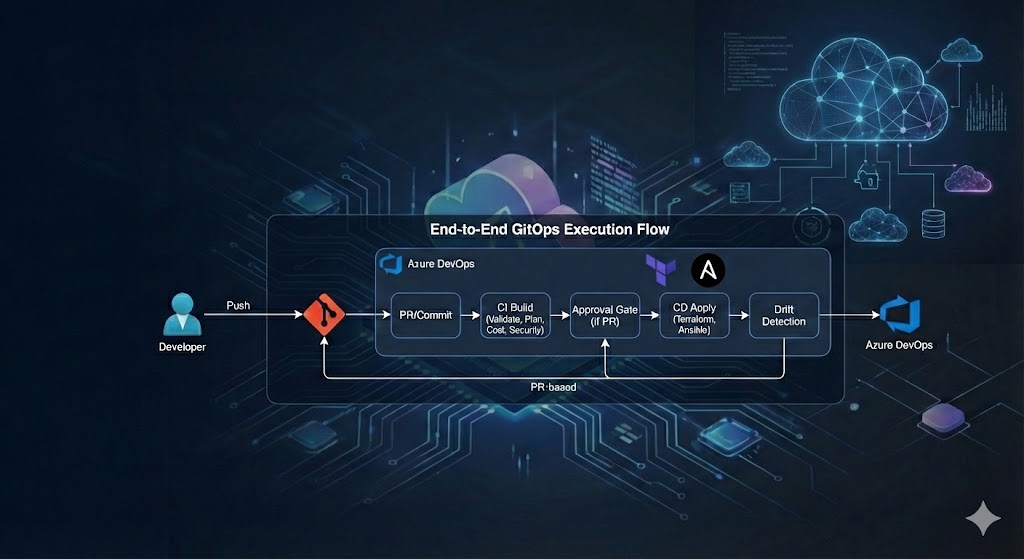
4. End-to-End GitOps Execution Flow
Below is the full lifecycle from developer intent to live infrastructure — fully automated, policy-driven, and auditable.
4.1 Developer Intent
- Developer clones application repo
- Creates feature branch from
main - Modifies Terraform root modules or Ansible config templates
Intent = code. No tickets, no portals, no consoles.**
4.2 Commit or Pull Request
Two execution models are supported:
| Model | Usage |
|---|---|
| Push-based | Non-prod, sandbox, dev environments |
| PR-based | Shared environments, prod |
Both use identical pipelines — only approval gates differ.
4.3 CI Build Stage (Always Runs)
Triggered by push or PR.
Includes:
- Secret scanning
- Formatting & linting
- Terraform init/validate/plan
- Cost estimation (Infracost)
- Artifact publication
Every change is dry-run before it can touch infrastructure.
4.4 Push-Based Execution (Direct Apply)
Used for:
- Dev
- Sandbox
- POCs
- Ephemeral environments
Flow:
- Build stage completes
- Apply stage executes automatically
- Terraform state updates
- Infrastructure converges
Push = speed with guardrails.
4.5 Pull Request-Based Execution (Approval Gated)
Used for:
- Shared environments
- Staging
- Production
Flow:
- CI build runs on PR
- Terraform plan + cost + scan results posted to PR
- Platform/app approvers review
- On merge → apply stage executes
PR = safety with velocity.
4.6 Drift Detection & Reconciliation
Nightly pipelines:
- Re-run Terraform plan
- Detect drift
- Alert or auto-remediate
Desired state always wins.
5. How Teams Use the Platform
This is how application teams interact with the platform — without touching pipelines or infrastructure internals.
5.1 Clone Application Repo
1
git clone https://tfs_serverName.com/tfs/IaC-CMA/tfcli-root-modules-workspace-repo/_git/demoapp
5.2 Modify Infrastructure Templates
- Add or update Terraform root modules
- Update Ansible host/group vars
- Follow naming conventions — automation depends on them
5.3 Create Feature Branch
1
2
3
4
git checkout -b feature-add-rhel-node
git add .
git commit -m "Add RHEL node for backend tier"
git push origin feature-add-rhel-node
5.4 Review Pipeline Feedback
PR automatically shows:
- Terraform plan diff
- Cost impact
- Security violations
- Policy violations
No guessing. No surprises.
5.5 Approve & Merge
Once approved:
- Pipeline auto-applies
- Infra converges
- State updated
- Artifacts archived
Teams declare intent. Platform executes safely.
6. Advanced GitOps Operating Models
Not all environments deserve the same risk model. Mature platforms support multiple execution modes.
6.1 Push-to-Deploy (Fast Path)
- Dev
- Sandbox
- Ephemeral
- Experimentation
Characteristics:
- No approvals
- Auto-apply
- Full guardrails
6.2 PR-to-Deploy (Standard Path)
- Shared environments
- Integration
- Staging
- Production
Characteristics:
- Mandatory review
- Policy enforcement
- Cost visibility
- Audit trail
6.3 Change-Controlled Deployment (Regulated Path)
- Banking
- Healthcare
- Gov workloads
Characteristics:
- External ticket reference required
- Manual approval gate
- Post-deploy validation stage
- Compliance artifact storage
One pipeline. Multiple execution contracts.
7. Platform Adoption at Scale
This is where most IaC programs fail — not technology, but adoption.
7.1 Treat the Platform as a Product
- Roadmap
- Backlog
- Release notes
- Support model
- Feedback loops
Platforms without product thinking become shelfware.
7.2 Default to Golden Paths
- Opinionated module templates
- Pre-approved architectures
- Pre-secured networking
- Standard tagging models
Most teams should never write infra from scratch.
7.3 Make the Right Thing the Easy Thing
- Zero pipeline YAML in app repos
- Zero backend config
- Zero provider config
- Zero state wiring
If using the platform is harder than bypassing it — teams will bypass it.
7.4 Shift Risk Left — Not Responsibility
Security, cost, and compliance should:
- Fail early
- Explain why
- Suggest fixes
- Never require tickets
Guardrails guide — they don’t block.
7.5 Enforce Idempotency Everywhere
- Terraform: repeatable plans
- Ansible: convergent playbooks
- Pipelines: re-runnable jobs
If reruns cause damage — automation isn’t safe yet.
8. Common Failure Modes (and How to Avoid Them)
| Failure | Root Cause | Fix |
|---|---|---|
| Pipeline sprawl | Teams copy YAML | Central templates |
| Snowflake modules | No contracts | Versioned core modules |
| Manual approvals everywhere | No risk model | Tiered execution paths |
| Drift chaos | No reconciliation | Scheduled drift detection |
| Slow adoption | Too much friction | Golden paths + automation |
9. What Success Looks Like
After adoption:
✅ App teams commit infra changes like app code
✅ Pipelines run without manual selection
✅ Security issues fail before apply
✅ Cost impact visible at PR time
✅ Production deploys are boring
✅ Platform team ships improvements weekly
✅ Drift becomes rare — and temporary
Success = Infrastructure becomes invisible again.
Closing Thoughts
Modern infrastructure automation is not about Terraform, pipelines, or GitOps tooling — it’s about turning infrastructure into a safe, scalable, self-service platform.
When done right:
- Developers ship faster
- Platforms stay stable
- Security shifts left
- Operations scales
- Audits become artifacts — not firefights
This is how IaC moves from scripting to systems engineering.
What’s Next
You’ve completed the DevOps and IaC Foundation series.
From here, you can explore:
- Multi-account landing zones
- Zero-trust networking automation
- Policy-as-code architectures
- Drift remediation engines
- Platform reliability engineering
- Or extend this foundation into Kubernetes, data platforms, or regulated workloads.